Building the correct security compliance is often a trial-and-error process. Many companies face their first audit, gather any documentation that is available, and design a framework that solves the short-term issue, not the long-term one.
When a second regulation applies two years later, they repeat the process. As a result, there are two parallel paths of compliance work that have nothing in common and that each cost twice as much.
A scalable framework is not a larger version of what you already have. It’s a different design, where a single control complies with several requirements at the same time, and new regulations fit in without having to start over.
Start with controls, not compliance targets
Many teams do this the wrong way around. They start with a standard – SOC 2, HIPAA, whatever a customer is demanding – and then try to shape their systems and processes into that standard. And every time a new standard gets introduced, they have to repeat the process.
The right way to go about it is to first develop a common controls library. Don’t ask “what does SOC 2 say we have to do to protect against this”; ask “what would a well-protected company do to protect against this,” and then map those controls back into each specific standard.
Access control policies, encryption practices, change management, incident response – these are not SOC 2 things. These are the things that SOC 2 (or any other audit) asks about that good protections already provide.
Do it this way and your access control policy reduces risk on day one. Then it also happens to help you pass seven different audits.
Also Read : Network Security Assessments: Safeguarding IT Infrastructure
Move access management to the object level
Perimeter-based security measures were enough to protect the data that was primarily stored within the confines of a building. However, this is no longer sufficient. The danger doesn’t just come from external actors. There is also the threat of lateral movement once an agent has breached the perimeter, and privileged accounts simply waiting to be compromised.
The principle of least privilege must be applied in earnest. This entails role-based restrictions at the level of individual data objects, not just network partitions. Zero trust architecture codifies this principle in system design, but its implementation version is much easier to apply: No one should have access they never actively need in their current role, and this access must be reconsidered on a regular basis rather than simply revoked if an agent departs.
This is the stage at which most companies are the least willing to spend. You apply IAM on implementation, assume all is well, and then abandon any kind of reassessment. This discrepancy between your officially documented access guidelines and the real allowance status will gradually increase, and it will probably come to light during an audit.
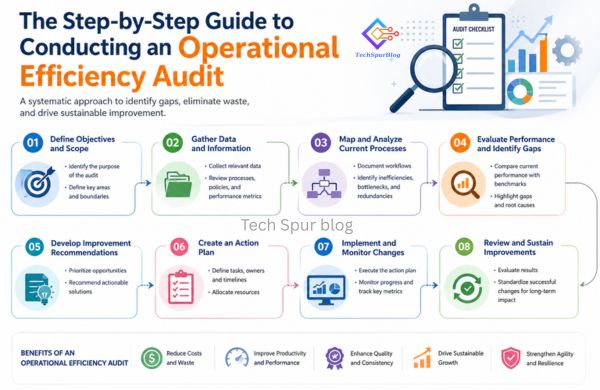
Map your processes to recognized control frameworks
Once you have a controls library, the next step is making sure each control maps clearly to audit requirements. This is the operational work that actually creates audit readiness.
Understanding soc 2 controls across the Trust Services Criteria – Security, Availability, Processing Integrity, Confidentiality, and Privacy – gives you a structured way to identify gaps. A gap analysis at this stage isn’t about finding problems to panic over.
It’s about understanding which of your existing controls satisfy criteria directly, which ones need documentation work, and which criteria aren’t covered yet.
Replace the annual audit sprint with continuous compliance
The fire drill approach to compliance, whereby nothing is done all year and then there’s a mad six-week rush to prepare and gather documentation, doesn’t effectively work. Not only is it incredibly stressful, but it also almost ensures that you’ll be facing an audit finding or two when it’s all said and done.
Those audit findings bring remediation plans, which are an unwelcome distraction to other planned security work. And with noncompliance tending to beget additional noncompliance, especially in environments with a lot of manual work and stretched-too-thin resources, the problem tends to get worse with each audit cycle.
Most problematic of all, from an org standpoint, is that compliance debt works a lot like technical debt does in that you end up paying for the shortcuts you took early on in terms of effort and energy later on. Fixing an audit finding isn’t as simple as just remediating the specific issue and calling it good.
It frequently requires an associated process change and possibly also some new monitoring to be sure the issue was truly addressed and stays that way going forward. That’s extra time, money, and energy out the door and work that could have, for the most part, been avoided.
The idea that doing whatever it takes to be declared “compliant” on the day of the auditor’s visit is an acceptable strategy for security isn’t simply flawed. It’s self-defeating.
Also Read : Data Privacy and Security: Protecting Your Information in the Digital World
Frame compliance as a sales asset
Executive buy-in is harder to maintain when security compliance is positioned as a cost. It’s easier when it’s positioned as a revenue enabler.
Companies with strong, documented security posture close enterprise deals faster because they can answer security questionnaires without delay. They pass vendor assessments without escalations. They don’t lose contracts because a SOC 2 report wasn’t available.
A compliance framework that’s built to scale gives the business something it can show prospects. That’s a different conversation than asking leadership to fund another audit cycle.
The companies that build this well aren’t thinking about security compliance as something that happens before a renewal. They’re treating it as infrastructure – something that runs continuously, adapts without breaking, and makes the rest of the business easier to operate.